The Embargo Is No Longer a Protection: What AI Is Changing in Responsible Disclosure
Six dnsmasq CVEs, a maintainer exhausted by the tsunami of AI-generated bug reports, and the public admission of a major doctrinal pivot. Reading a weak signal that could foreshadow the end of a model thirty years old.
On May 11, 2026, Simon Kelley published six CVEs for dnsmasq. He also published, without naming it, the end of an era. In the same message, the maintainer of the software that serves as the DNS and DHCP Swiss Army knife for millions of routers announced that he is abandoning long disclosure embargoes. The reason is more structurally worrying than the vulnerabilities themselves: AI now produces so many bug reports that the rarity of discovery, the hidden foundation of responsible disclosure, no longer exists.
Six CVEs, and a message that says more than the list
On May 11, 2026, Simon Kelley published on the dnsmasq-discuss mailing list a message titled Security – IMPORTANT (1). He announces the simultaneous disclosure of six vulnerabilities affecting dnsmasq, the lightweight server combining DNS, DHCP, TFTP and network boot functions, present in a significant portion of the global fleet of routers, Wi-Fi access points, embedded Linux distributions, Pi-hole deployments and OpenWrt gateways. Coordinated through CERT/CC under note VU#471747 (2), the disclosure is accompanied by the immediate publication of dnsmasq 2.92rel2 and the promise of a stable 2.93 within the following week.
The six identifiers cover a broad technical range: an unauthenticated heap buffer overflow in extract_name() enabling cache poisoning or denial of service (CVE-2026-2291), two critical DNSSEC parser bugs leading respectively to an infinite loop and a memory leak (CVE-2026-4890 and CVE-2026-4891), a heap-based out-of-bounds write in the DHCPv6 implementation allowing arbitrary code execution with dnsmasq process privileges via an oversized CLIENT_ID (CVE-2026-4892), a bypass of source checks through the EDNS Client Subnet mechanism of RFC 7871 (CVE-2026-4893), and a buffer overflow in extract_addresses() exploitable via a malformed DNS response (CVE-2026-5172) (3)(4).
The most complete technical analysis is published by xchglabs (5), whose researcher Royce M is credited for five of the six discoveries. The public PoC for CVE-2026-2291 and CVE-2026-4892 demonstrates that the attacks are reproducible with a self-contained Python harness. The operational severity is high: CVE-2026-4890 is rated 7.5 HIGH on CVSS 3.1, and CVE-2026-2291 requires neither authentication nor DNSSEC, only that dnsmasq follow a CNAME chain to an attacker-controlled authoritative server, which is the default forwarder behavior.
Major distributions published their patched packages within hours of disclosure. Debian DSA-6264-1 covers bookworm and trixie (6). Ubuntu USN-8268-1 covers all supported versions from 16.04 LTS through 26.04 LTS (7). SUSE, Red Hat and community distributions followed the same compressed timeline.
This first reading, factual and technical, is the one found in most of the dispatches published the week of May 12. It is complete. It is accurate. And it misses the real event.
The CVD doctrine: genealogy of a now-fragile assumption
Coordinated Vulnerability Disclosure, known as CVD, rests on a model stabilized since the early 2000s. A researcher discovers a flaw. The researcher informs the vendor. An embargo period is negotiated, generally between 60 and 120 days, during which technical details remain confidential. The vendor prepares a patch. At the embargo’s expiration, the vulnerability and its patch are published simultaneously. Users thus have protection before details become publicly exploitable.
This model rests on an assumption rarely stated but structurally decisive: the rarity of discovery. If a vulnerability is so rare that the researcher who reports it is probably the only one, or one of very few, to have found it, then the embargo genuinely protects users. The average attacker does not have this information during the embargo period. The model works.
This assumption has always been imperfect. Intelligence services have long held advanced discovery capabilities. Commercial exploit vendors, including Zerodium, Crowdfense or various state actors, buy and stockpile zero-days that vendors ignore. But these actors represented marginal cases, sufficiently rare for the doctrine to remain operational at global scale.
What changes in 2026 is not the nature of this imperfection, but its order of magnitude. The arrival of language models trained on code, capable of assisted fuzzing, of generating PoCs from textual descriptions, and of comparing millions of known vulnerable patterns to arbitrary codebases, transforms rarity into near-absence. If ten researchers each equipped with an AI agent can identify the same bug in parallel within a few days, then the 90-day embargo ceases to protect users and begins to expose them: while the vendor prepares its patch, actors with the same tools have an operational window of several weeks.
The CVD doctrine was designed for a world in which discovering a vulnerability was an event costly in human time and expertise. When this cost collapses, the rarity assumption underlying the embargo no longer holds. It is this finding, expressed for the first time so clearly by the maintainer of critical software, that makes Simon Kelley’s message a historic weak signal.
Three admissions in a single message
Simon Kelley’s email contains several sentences that deserve to be quoted in full. Taken together, they constitute first-hand testimony on the actual state of responsible disclosure in 2026.
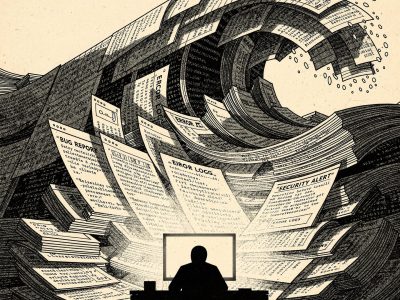
First admission, the operational fatigue of a sole maintainer overwhelmed by volume:
What this sentence says, behind the apparent sobriety of the British tone, is that dnsmasq, infrastructure software used on tens of millions of machines, is maintained by a person currently drowning in automated reports. The word duplicates is revealing: it signals that several AI-assisted researchers converge on the same patterns, which empirically confirms the loss of rarity discussed above.
Second admission, the explicit formalization of the doctrinal pivot:
The sentence is posed as nearly self-evident. Yet it announces a rupture. When the good guys are numerous enough that the maintainer loses count, then the probability that the bad guys have already found becomes sufficiently high that the embargo ceases to protect. The doctrine reverses: rapid public disclosure becomes a strategy for reducing informational asymmetry, and no longer a betrayal of the user. This is exactly the reasoning made by certain full disclosure advocates in the 1990s, but issued this time by a maintainer traditionally attached to coordination.
Third admission, the structural and durable dimension of the phenomenon:
The term tsunami is not innocent in Simon Kelley’s measured prose. It signals that the maintainer is not handling a cyclical peak but a structural wave he anticipates as permanent. The promise that this process will be repeated soon implies that the classical pace of security releases, based on quarterly or biannual cycles, is itself obsolete. The frequency of Patch Days becomes continuous.
Why now: anatomy of the tsunami
The phenomenon Simon Kelley describes is not isolated. It is part of a broader transformation that has accelerated over the past eighteen months. Three factors converge.
The first is tool availability. Language models capable of reasoning over code are now accessible at low marginal cost. An AI agent combining an LLM, a fuzzer, and a known pattern analysis system can be deployed by an individual researcher on a monthly budget lower than that of a high-end workstation. The barrier to entry for serious vulnerability research has collapsed. The specialized commercial teams that dominated this market for fifteen years now find themselves competing with independent researchers equipped with comparable, or identical, tools.
The second factor is the qualitative improvement of results. LLMs no longer merely flag suspicious patterns; they produce contextual analyses, identify trigger conditions, generate functional PoCs, and formulate readable reports. A maintainer can no longer dismiss an AI report at a glance by spotting naive generation artifacts. The average quality of an AI report in 2026 is comparable to a human report produced by a junior researcher, with the advantage of infinitely greater volume.
The third factor is the absence of upstream filtering. Where commercial bug bounty programs have industrial triage processes, open-source projects maintained by one to three people receive the tsunami without intermediary. Triage becomes the maintainer’s main job, at the expense of development and actual remediation.
The word duplicates used by Simon Kelley is the most important statistical indicator in his message. When multiple AI researchers independently converge on the same bug, it empirically demonstrates that discovery is no longer rare. This convergence stands as proof that the rarity doctrine underlying the classical embargo has ceased to be operational. The duplicate is no longer an administrative inconvenience; it is a quantitative measure of the model’s erosion.
Adding to these technical factors is an economic dynamic. Competition among AI actors, whether independent researchers, commercial teams or academic labs, creates an incentive for rapid disclosure for reasons of reputation and credit. Waiting 90 days while another researcher publishes the same bug first means losing attribution. The rational calculation now leans toward accelerated publication, which exerts additional pressure on maintainers and vendors.
A signal that resonates with other ruptures
Simon Kelley’s message is not the only recent indicator of a crisis in responsible disclosure. The previous week, the uncoordinated public disclosure of Windows zero-days YellowKey and GreenPlasma by researcher Chaotic Eclipse (8) illustrated another form of rupture: a researcher voluntarily abandoning the CVD model to protest Microsoft’s silent patching practices. The two cases share a common structure. An actor in the responsible disclosure chain, a maintainer in one case, a researcher in the other, acknowledges that the model no longer works according to its own rules, and unilaterally adapts practice.
The motivations differ. Simon Kelley pivots for operational reasons: submersion by volume makes embargo costly and poorly protective. Chaotic Eclipse pivots for ethical reasons: silent patching, in their view, betrays the principle of transparency that grounds trust in coordination. But the result is the same: an act of public defection from the CVD model, motivated by the conviction that it no longer fulfills the function it claims to ensure.
These two weak signals, five days apart, suggest that the CVD doctrine is entering a phase of contestation that no longer belongs to theoretical debates among experts but to practical adaptations by concerned actors. When a historical maintainer abandons long embargoes through operational exhaustion, and an experienced researcher abandons full CVD through distrust, the model loses its two base supporters: the one who maintains and the one who discovers. It is not certain the model will survive in its current form.
Operational implications for organizations
For security teams, what the dnsmasq case reveals goes beyond the immediate need to patch. Three operational consequences deserve to be anticipated.
Compression of patching windows
If long embargoes disappear in favor of rapid or immediate disclosures, the delay between CVE publication and actual exploitation mechanically shrinks. Organizations operating on monthly or quarterly patching cycles will have to accept a higher frequency, or assume increased risk between two maintenance windows. Virtual patching tools and WAFs become structural complements rather than temporary palliatives.
Increased noise in CTI feeds
The tsunami of bug reports described by Simon Kelley will translate into a significant increase in the number of CVEs published each quarter. CTI teams will need to sharpen their prioritization capabilities to distinguish structuring vulnerabilities, those with proven or imminent exploitation, from mass CVEs discovered by automated fuzzing whose exploitation remains theoretical. The CVSS metric alone becomes insufficient. Indicators such as EPSS, CISA KEV catalog, and active exploitation intelligence become the operational sorting criteria.
Pressure on bug bounty programs
Internal or outsourced bug bounty programs will face the same tsunami. The value of an isolated AI report tends toward zero, but the processing cost remains high. Reward models will have to evolve to value analysis quality and demonstrated exploitability rather than mere detection. Some major actors have already adjusted their scales in this direction in 2025 and 2026.
For organizations operating dnsmasq directly or indirectly, the immediate action is deployment of version 2.92rel2, pending stable 2.93. Concerned environments include OpenWrt routers, Pi-hole servers, custom Linux gateways, small-subsidiary DHCP infrastructure, and embedded distributions. The perimeter is typically under-mapped in traditional asset management tools.
Toward what new doctrine?
The erosion of CVD does not mean the absence of doctrine. It opens a period of recomposition whose contours are beginning to take shape. Three paths emerge from ongoing technical discussions, none yet reaching consensus status.
The first path is that of short and differentiated embargoes. Rather than a standard 90-day delay, some actors propose adaptive windows, short for bugs detectable by automated fuzzing (and therefore probably already discovered elsewhere), long only for vulnerabilities requiring hard-to-replicate human expertise. This approach amounts to formalizing what Simon Kelley does empirically: sorting bugs based on their probability of being discovered in parallel.
The second path is public disclosure with synchronous patches. Rather than waiting for long embargoes, the vendor publishes the patch and the description simultaneously as soon as technically possible, accepting the short window between publication and client deployment. This approach already exists for certain products, notably in the Linux kernel world where security through openness is doctrinal. It imposes, however, near real-time deployment capability on downstream clients, whose maturity remains uneven.
The third path, more disruptive, is the pooling of triage costs. If the AI bug report tsunami overwhelms individual maintainers, several foundation projects are considering shared triage services funded by industrial users. This path raises questions of governance, confidentiality of in-progress reports, and economic sustainability, but it has the merit of directly addressing the capacity problem.
Whatever path prevails, Simon Kelley’s email of May 11, 2026 will remain a marker. For the first time, a maintainer of major infrastructure software publicly stated, in the dry language of technical announcements, that responsible disclosure as it had existed for thirty years no longer holds. This sentence, slipped between two paragraphs about the 2.93rc1 tag, will have more medium-term consequences than the six CVEs it accompanies.
Security teams, CISOs, CTI leaders and architects who rely on disclosure cycle predictability to plan their operations must integrate now that this predictability is disappearing. Not through political decision, not through spectacular rupture, but through an operational tipping point acted on a May evening by an exhausted British maintainer. This is often how eras end.